| Ⅰ | This article along with all titles and tags are the original content of AppNee. All rights reserved. To repost or reproduce, you must add an explicit footnote along with the URL to this article! |
| Ⅱ | Any manual or automated whole-website collecting/crawling behaviors are strictly prohibited. |
| Ⅲ | Any resources shared on AppNee are limited to personal study and research only, any form of commercial behaviors are strictly prohibited. Otherwise, you may receive a variety of copyright complaints and have to deal with them by yourself. |
| Ⅳ | Before using (especially downloading) any resources shared by AppNee, please first go to read our F.A.Q. page more or less. Otherwise, please bear all the consequences by yourself. |
| This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License. |
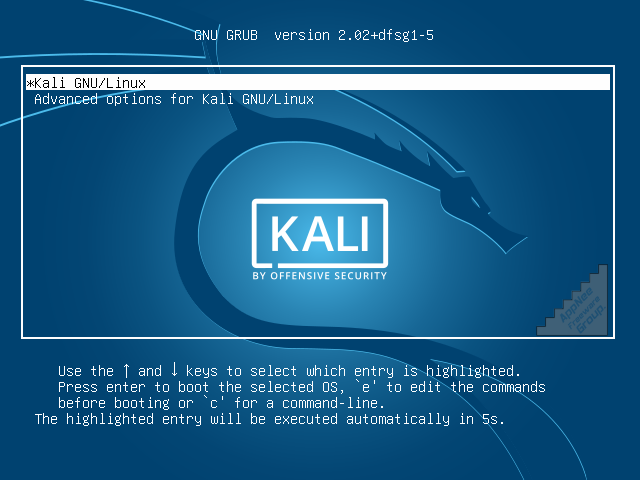
Kali Linux (successor of BackTrack Linux) is a free and open-source Debian-based Linux distribution funded and maintained by Offensive Security from Switzerland. Users can boot and use this OS via hard disk, live CD or live USB anytime and anywhere. Almost all open-source tools used for digital forensics, penetration testing, ethical hacking and network security assessments are included. There is no need to prepare and maintain this Linux distribution (including gathering all those software and their dependencies) by yourself, or to install any software and save any files on Kali.
Continue reading Kali Linux – Most advanced Linux distro for penetration testing and ethical hacking