| Ⅰ | This article along with all titles and tags are the original content of AppNee. All rights reserved. To repost or reproduce, you must add an explicit footnote along with the URL to this article! |
| Ⅱ | Any manual or automated whole-website collecting/crawling behaviors are strictly prohibited. |
| Ⅲ | Any resources shared on AppNee are limited to personal study and research only, any form of commercial behaviors are strictly prohibited. Otherwise, you may receive a variety of copyright complaints and have to deal with them by yourself. |
| Ⅳ | Before using (especially downloading) any resources shared by AppNee, please first go to read our F.A.Q. page more or less. Otherwise, please bear all the consequences by yourself. |
| This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License. |

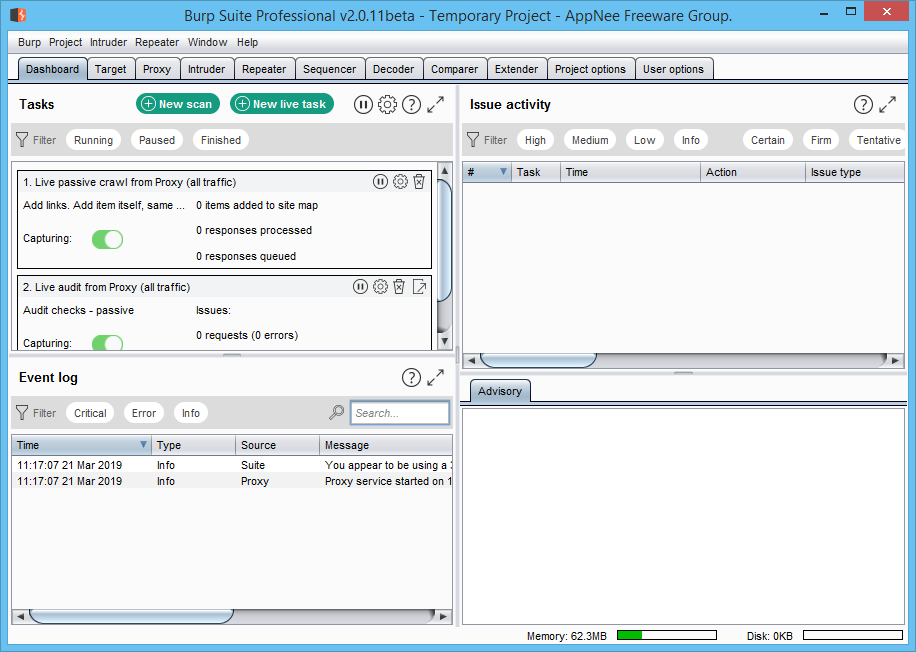
Burp Suite (Burp for short) is a well-known and popular integrated tools platform that is used to perform security penetration tests for web applications (actually it’s more commonly used for hacking activities such as web attacks), written in Java, developed by PortSwigger from United Kingdom.
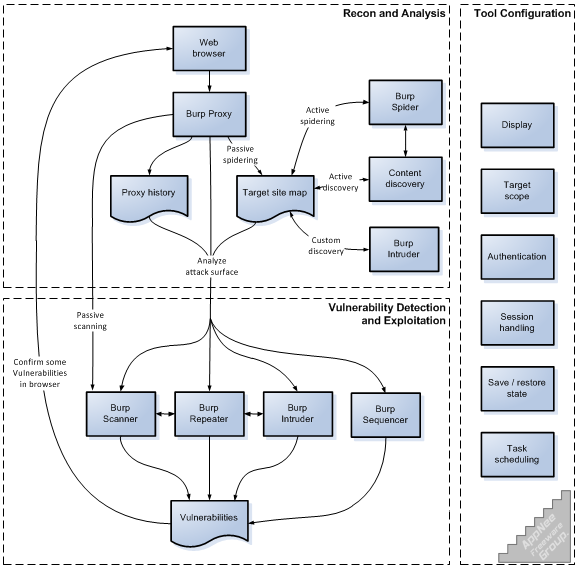
Burp Suite includes a number of tools for network attacks, and many interfaces have been designed for these tools, in order to facilitate and speed up the process of attacking applications. All tools share a powerful, extensible framework, which can process and display HTTP messages, persistence, certification, proxy, log, alert, etc. Its diverse functions can help us perform various tasks, including the interception and modification to network requests, scanning the vulnerabilities of web applications, cracking the login form with brute force, perform session, token and other random inspections.
In summary, as one of the best tools for security testing of Web applications, Burp Suite is a difficult place to get started, especially with its complex parameters. But once you get the hang of its usage, it will definitely make you even more powerful in daily work.
// Contained Tools //
| Tool | Description |
| HTTP Proxy | It operates as a web proxy server, and sits as a man-in-the-middle between the browser and destination web servers. This allows the interception, inspection and modification of the raw traffic passing in both directions. |
| Scanner | A web application security scanner, used for performing automated vulnerability scans of web applications. |
| Intruder | This tool can perform automated attacks on web applications. The tool offers a configurable algorithm that can generate malicious HTTP requests. The intruder tool can test and detect SQL Injections, Cross Site Scripting, parameter manipulation and vulnerabilities susceptible to brute-force attacks. |
| Spider | A tool for automatically crawling web applications. It can be used in conjunction with manual mapping techniques to speed up the process of mapping an application’s content and functionality. |
| Repeater | A simple tool that can be used to manually test an application. It can be used to modify requests to the server, resend them, and observe the results. |
| Decoder | A tool for transforming encoded data into its canonical form, or for transforming raw data into various encoded and hashed forms. It is capable of intelligently recognizing several encoding formats using heuristic techniques. |
| Comparer | A tool for performing a comparison (a visual “diff”) between any two items of data. |
| Extender | Allows the security tester to load Burp extensions, to extend Burp’s functionality using the security testers own or third-party code (BAppStore) |
| Sequencer | A tool for analyzing the quality of randomness in a sample of data items. It can be used to test an application’s session tokens or other important data items that are intended to be unpredictable, such as anti-CSRF tokens, password reset tokens, etc. |
// System Requirements //
- Java Runtime Environment (JRE)
- Java Development Kit (JDK)
// Edition Statement //
AppNee provides the Burp Suite Professional Edition multilingual full installers and loader & keygen for Windows 32-bit & 64-bit.
// Installation Notes //
for v2024.1.1+:
- Double click “Burp_License_Cleaner.reg” to import
- Run “BurpLoaderKeygen117.jar“, input any license text you like, copy the license, and click ‘Run‘
- Paste the license key, and click ‘Next‘
- Click ‘Manual activation‘
- Click ‘Copy request‘, paste it into keygen’s “Activation Request” field, and copy the generated “Activation Response”
- Back to program, click ‘Paste response‘, and click ‘Next‘
- Always run program from the Loader & Keygen
- Done
*** Do not copy program “burpsuite_pro_v20xx.x.x.x.jar” to other location, all files should be in the same folder.
for v2022.9:
- Run the loader to start program
for v1.7.37/v2.1.04/v2020.x+:
- Download and extract program
- Run the loader & keygen
- Input any “License Text” you like, copy the “License“, and click ‘Run‘
- Accept the agreement, then paste the license key, and click ‘Next‘
- Click ‘Manual activation‘
- Click ‘Copy request‘, and paste it back to loader & keygen’s “Activation Request” field
- Copy the generated “Activation Response” back to the Manual Activation window, click ‘Paste response‘, then click ‘Next‘ and ‘Finish‘
- Done
*** Use the loader & keygen to launch program (by clicking the ‘Run‘ button) every time.
// Related Links //
// Download URLs //
| License | Version | Download | Size |
| Community Edition (free) | Latest |  |
n/a |
| Professional Edition | v2024.2.1 |  |
527 MB |
(Homepage)
| If some download link is missing, and you do need it, just please send an email (along with post link and missing link) to remind us to reupload the missing file for you. And, give us some time to respond. | |
| If there is a password for an archive, it should be "appnee.com". | |
| Most of the reserved downloads (including the 32-bit version) can be requested to reupload via email. |