| Ⅰ | This article along with all titles and tags are the original content of AppNee. All rights reserved. To repost or reproduce, you must add an explicit footnote along with the URL to this article! |
| Ⅱ | Any manual or automated whole-website collecting/crawling behaviors are strictly prohibited. |
| Ⅲ | Any resources shared on AppNee are limited to personal study and research only, any form of commercial behaviors are strictly prohibited. Otherwise, you may receive a variety of copyright complaints and have to deal with them by yourself. |
| Ⅳ | Before using (especially downloading) any resources shared by AppNee, please first go to read our F.A.Q. page more or less. Otherwise, please bear all the consequences by yourself. |
| This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License. |
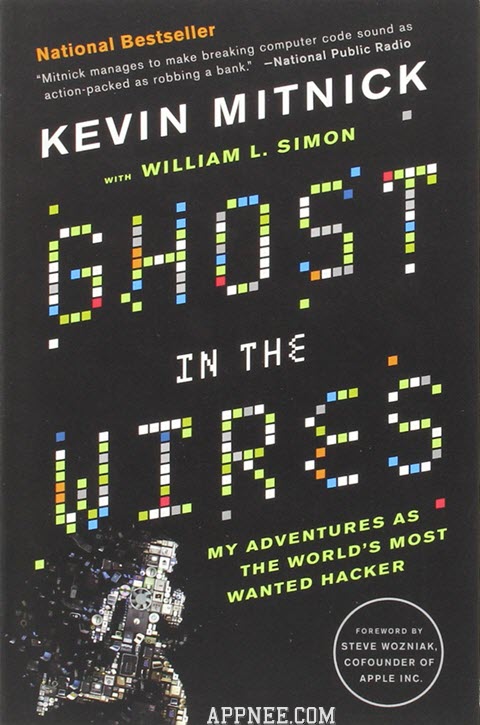
Kevin Mitnick is referred to as “The world’s first-rate hacker”, his legendary life and hacking experience have become topic that industry and major news media take delight in talking about. Of course the present Mitnick (gave up evil and returned to good) has become the world’s famous white hat hacker, he uses his own experience to guide the well-known enterprises and organizations to enhance their safety and protection measures.
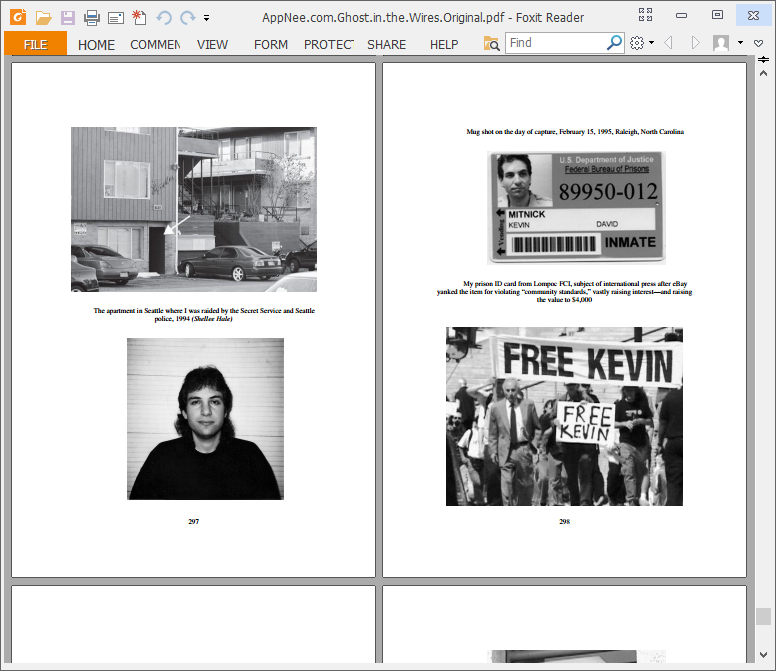
Ghost in the Wires: My Adventures as the World’s Most Wanted Hacker, in fact, is Mitnick’s autobiography. In this book, he looked back on his hacking journey with ups and downs of the plot – even not second to a good detective novel (the particularly fascinating part is the inner monologue when Kevin knew the danger was approaching). We have to admit that Mitnick had played the social engineering to the extreme), the pursuit of technology and sense of achievement really gave every reader a deepgoing impression.
Because the background of the story was in the age that Internet just started, whose network technology is surely far worse than now. But it is important to let you know 3 things – First, no matter how strong the security systems are, they also have holes all the time; Second, the most problematic factor will always be the human (rather than the computer); Finally, after all, the so-called social engineering is just the art of deception!
BTW, it has a piece of cipher text at the beginning of each chapter in this book, people who are interested can try to crack, or you can Google that with ease.
// Download URLs //
| Type | Format | Download | Size |
| Original |  |
2.69 MB | |
| Converted |  |
2.75 MB | |
| Original | MOBI |  |
1.23 MB |
(Homepage)
| If some download link is missing, and you do need it, just please send an email (along with post link and missing link) to remind us to reupload the missing file for you. And, give us some time to respond. | |
| If there is a password for an archive, it should be "appnee.com". | |
| Most of the reserved downloads (including the 32-bit version) can be requested to reupload via email. |