| Ⅰ | This article along with all titles and tags are the original content of AppNee. All rights reserved. To repost or reproduce, you must add an explicit footnote along with the URL to this article! |
| Ⅱ | Any manual or automated whole-website collecting/crawling behaviors are strictly prohibited. |
| Ⅲ | Any resources shared on AppNee are limited to personal study and research only, any form of commercial behaviors are strictly prohibited. Otherwise, you may receive a variety of copyright complaints and have to deal with them by yourself. |
| Ⅳ | Before using (especially downloading) any resources shared by AppNee, please first go to read our F.A.Q. page more or less. Otherwise, please bear all the consequences by yourself. |
| This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License. |
HijackThis (AKA: Trend Micro HijackThis, HJT for short) was once one of the most popular malicious code, virus scanning and fixing utility for advanced PC users. Originally written in Visual Basic by a student named Merijn Bellekom in Netherlands using his spare time. It opened source after acquisition by Trend Micro company in 2007.
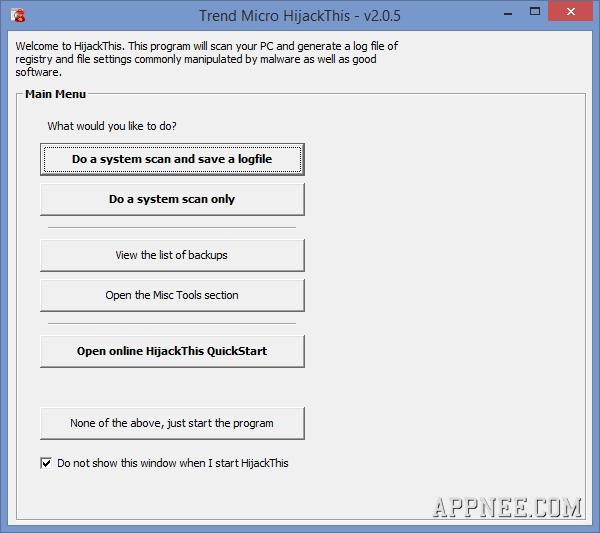
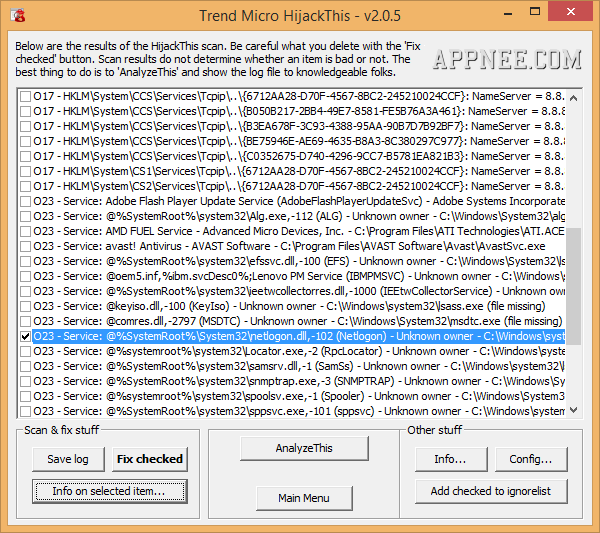
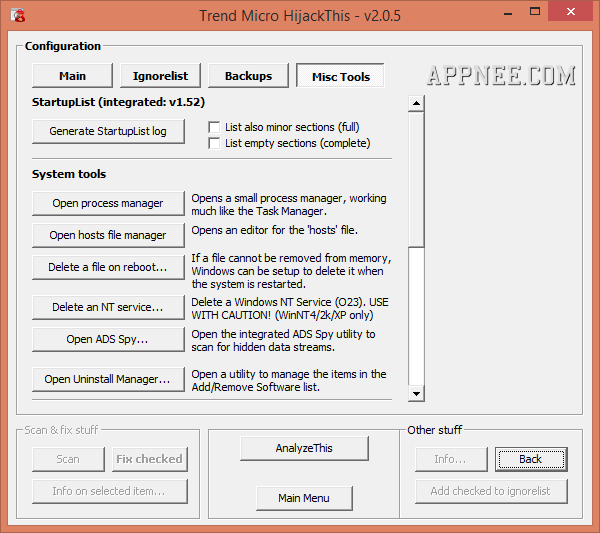
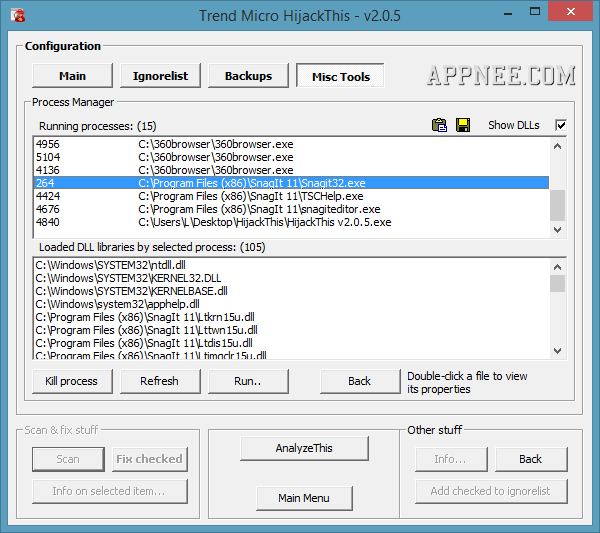
HijackThis can scan and generate a detailed report of Windows system registry and specific file configurations. But it itself does not make a judgment of safe or dangerous to the scan results, which means that it requires the users themselves to analyze, judge, you can not hastily deal with them. In addition, HijackThis also provides several auxiliary tools used to further help you manually remove the identified malware or virus.
HijackThis’s scan range is very comprehensive, and it can repair most malicious modifications. In particular, HijackThis allows to keep the scan results as a log file and open it with notepad directly. By doing so, for beginner users, they can choose to post the log file to online forums, in order to facilitate enthusiasts to help solve the problems.
// Key Features //
- Lists the contents of key areas of the registry and hard drive
- Generate reports and presents them in an organized fashion
- Does not target specific programs and URLs
- Detects only the methods used by hijackers
- Can be set for automatically scan at system boot up
- Short log
- Fast scan
- No need to script for fixing
- No need internet or constant database updates
- Well-familiar to many people
- Portable
// Prompts //
- There is a number in front of each suspicious item, and in fact these numbers represent different meanings. If you want to see their corresponding information, please click on the “Info” button in the main window.
// Warning //
- HijackThis does not determine what is good or bad. Do not make any changes to your computer settings unless you are an expert computer user.
// Related Links //
// Download URLs //
| License | Version | Download | Size |
| HijackThis | |||
| Freeware | Latest |  |
n/a |
| HiJackThis Fork (by Dragokas) | |||
| Freeware | Latest |  |
n/a |
(SourceForge | GitHub)
| If some download link is missing, and you do need it, just please send an email (along with post link and missing link) to remind us to reupload the missing file for you. And, give us some time to respond. | |
| If there is a password for an archive, it should be "appnee.com". | |
| Most of the reserved downloads (including the 32-bit version) can be requested to reupload via email. |