| Ⅰ | This article along with all titles and tags are the original content of AppNee. All rights reserved. To repost or reproduce, you must add an explicit footnote along with the URL to this article! |
| Ⅱ | Any manual or automated whole-website collecting/crawling behaviors are strictly prohibited. |
| Ⅲ | Any resources shared on AppNee are limited to personal study and research only, any form of commercial behaviors are strictly prohibited. Otherwise, you may receive a variety of copyright complaints and have to deal with them by yourself. |
| Ⅳ | Before using (especially downloading) any resources shared by AppNee, please first go to read our F.A.Q. page more or less. Otherwise, please bear all the consequences by yourself. |
| This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License. |
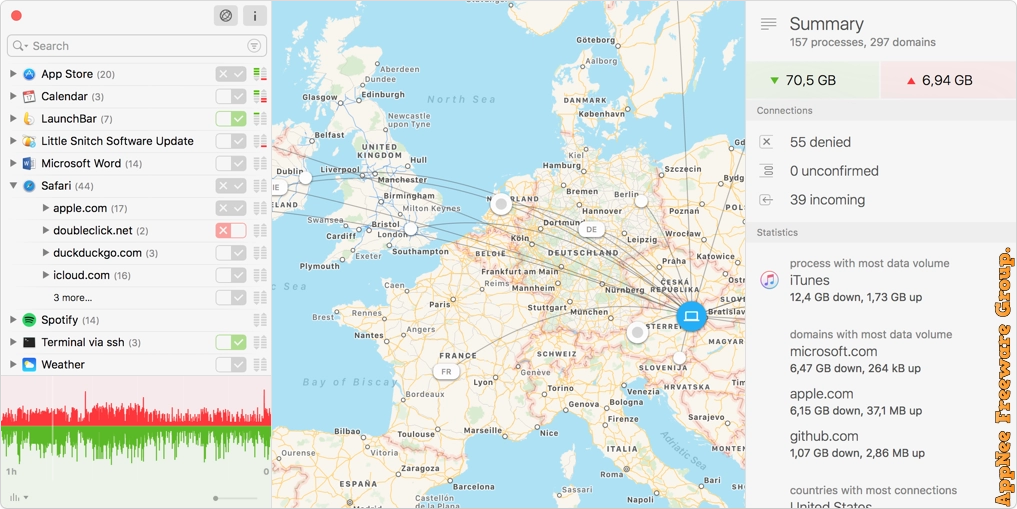
When your Mac computer is connected to the Internet, countless connections will be quietly built in the background. Once some application connects to the Internet, it can send any information that it wants to send to any place in the world. In order to monitor these connections, better maintain our privacy security, and especially withstand the tracking software, Trojans, or other types of malware, we usually have to use the boring and difficult to use firewall software. Even worse, the inbuilt firewall program of Mac OS is only able to control incoming connections, has no monitoring and controlling capabilities for outgoing connections.
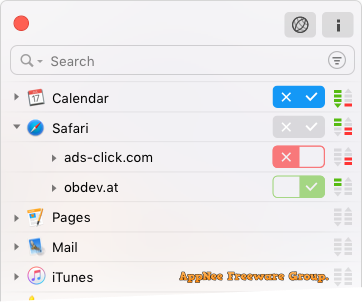
Little Snitch is an excellent, easy-to-use and trustworthy personal firewall software for Mac, developed by Objective Development Software from Austria, written in Objective-C. It can be used to monitor and prevent any network connection (both inbound and outbound) generated by the specified software. For example, when you launch some software, Little Snitch will remind users to allow it to connect to Internet or not. If you have a lot of confidential data stored on your Mac, it’s very necessary to install a user friendly firewall like Little Snitch. It reminds you of all inbound/outbound network connection requests in real time, so as to protect the safety of user’s computer effectively, and prevent applications from secretly accessing the network and sending data to the outside.
Once you connect to the Internet, the application may optionally send any thing they want. In most cases, they will bring you a lot of benefits. But for some software, what they do to us is opposite, such like tracking software, Trojan, or other malicious software. The trouble is that you didn’t notice anything about what and how they are doing, because all of this is conducted secretly. This case, Little Snitch can make any network/Internet connections sleep with the lights on (from invisible to visually visible), and enables you to control everything!
// Key Features //
| Feature | Description |
| Real-time Traffic Diagram | A detailed traffic history of the last hour provides a powerful tool for analyzing individual data connections. |
| Corresponding rule | Figure out quickly why a particular connection was allowed or denied. |
| Snapshots | Save a snapshot of the current status of all connections for later analysis. |
| Simplified connection list | Connections are grouped by domain (e.g. apple.com or google.com) for easy navigation. |
| Dark or light appearance | Choose the appearance that best matches your personal taste. |
| Statistics | Discover processes and servers creating the highest data volume and much more. |
| Improved inspector | Now with integrated Research Assistant, code signature check and geographic information. |
| Quick filters and location search | Search for specific locations, or focus on all denied connections using the filters menu. |
| Data volumes and bandwidth | Observe the data volume and bandwidth per process, domain or server. |
// System Requirements //
- macOS 10.11+
// Universal Serial Numbers //
| Serial Number (not verified) |
| 32R37B1240-722M9-JZ39DNXFAM |
| 34RSCTGAU1-715LS-23Y6P91MEB |
| 35TFJTSW10-715NS-MXBM13FLTS |
// Edition Statement //
AppNee provides the Little Snitch multilingual full installers, and all versions universal serial numbers for Mac.
// Tips //
- You can selectively let familiar software free access the Internet, and limit the activities of applications that don’t need Internet connection or you don’t know what they are and where they are from to local (i.e.: offline use). Thus, you will be able to turn passive defense into active defense even in the face of all sorts of known or unknown Trojans or viruses.
- Look at it another way, you can also use a firewall program to organize and control the license network verification mechanism of many software, in order to assist the software cracking process.
// Download URLs //
| Version | Download | Size |
| v5.7.3 |  |
32.3 MB |
(Homepage)
| If some download link is missing, and you do need it, just please send an email (along with post link and missing link) to remind us to reupload the missing file for you. And, give us some time to respond. | |
| If there is a password for an archive, it should be "appnee.com". | |
| Most of the reserved downloads (including the 32-bit version) can be requested to reupload via email. |