| Ⅰ | This article along with all titles and tags are the original content of AppNee. All rights reserved. To repost or reproduce, you must add an explicit footnote along with the URL to this article! |
| Ⅱ | Any manual or automated whole-website collecting/crawling behaviors are strictly prohibited. |
| Ⅲ | Any resources shared on AppNee are limited to personal study and research only, any form of commercial behaviors are strictly prohibited. Otherwise, you may receive a variety of copyright complaints and have to deal with them by yourself. |
| Ⅳ | Before using (especially downloading) any resources shared by AppNee, please first go to read our F.A.Q. page more or less. Otherwise, please bear all the consequences by yourself. |
| This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License. |
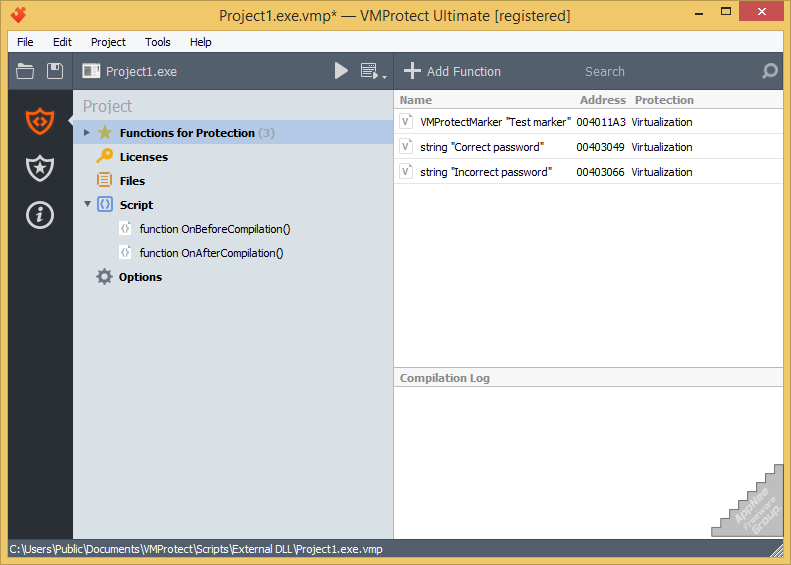
In the current Internet environment, most commercial software can be cracked, and that is just a matter of cost and time at most. In order to protect their software from reverse engineering or cracking, almost all software developers use a lot of codes with complex encryption algorithms. That not only costs developers a lot of energy and expense, but also makes the program more chaotic and bloated, and the final effect is not obvious.
Continue reading [v3.0.4] Themida – Advanced Windows software protection system