| Ⅰ | This article along with all titles and tags are the original content of AppNee. All rights reserved. To repost or reproduce, you must add an explicit footnote along with the URL to this article! |
| Ⅱ | Any manual or automated whole-website collecting/crawling behaviors are strictly prohibited. |
| Ⅲ | Any resources shared on AppNee are limited to personal study and research only, any form of commercial behaviors are strictly prohibited. Otherwise, you may receive a variety of copyright complaints and have to deal with them by yourself. |
| Ⅳ | Before using (especially downloading) any resources shared by AppNee, please first go to read our F.A.Q. page more or less. Otherwise, please bear all the consequences by yourself. |
| This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License. |
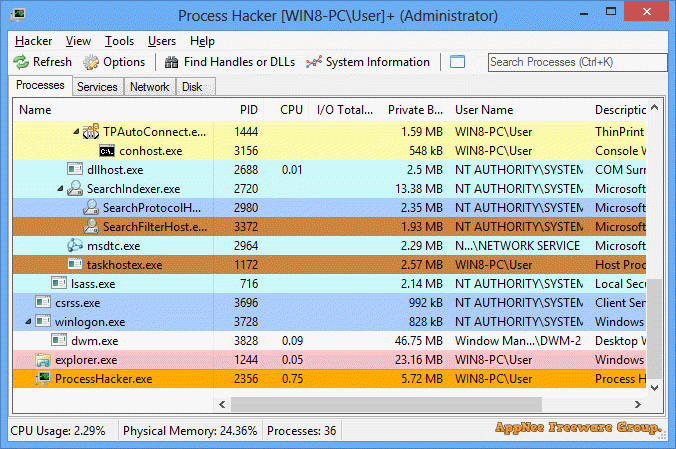
Today’s viruses, trojans and many other malicious software are much smarter and more shrewd than ever before. In other words, the traditional methods of identifying suspicious processes such like by checking the startup items have been far from enough. For example, they have been used to embed themselves into system processes, inject into driver files, disguise as system services, and so on, so as to implement autorun and bypass the scanning and killing of most anti-virus software. As a consequence, we could see that more and more antivirus software AIDS came into popular.
Continue reading Process Hacker – Advanced alternative of Windows Task Manager