| Ⅰ | This article along with all titles and tags are the original content of AppNee. All rights reserved. To repost or reproduce, you must add an explicit footnote along with the URL to this article! |
| Ⅱ | Any manual or automated whole-website collecting/crawling behaviors are strictly prohibited. |
| Ⅲ | Any resources shared on AppNee are limited to personal study and research only, any form of commercial behaviors are strictly prohibited. Otherwise, you may receive a variety of copyright complaints and have to deal with them by yourself. |
| Ⅳ | Before using (especially downloading) any resources shared by AppNee, please first go to read our F.A.Q. page more or less. Otherwise, please bear all the consequences by yourself. |
| This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License. |
As a matter of fact, the USB flash drive is the very breeding ground for most viruses/trojans today. They (including the famous WannaCry ransomware attack) initially infect portable storage devices, then spread across the entire LAN, and finally seize any networking opportunity to spread themselves to the Internet. On the other hand, they usually move from the USB device to some key nodes of LANs, which leads to the network paralysis and Internet disaster in the end.
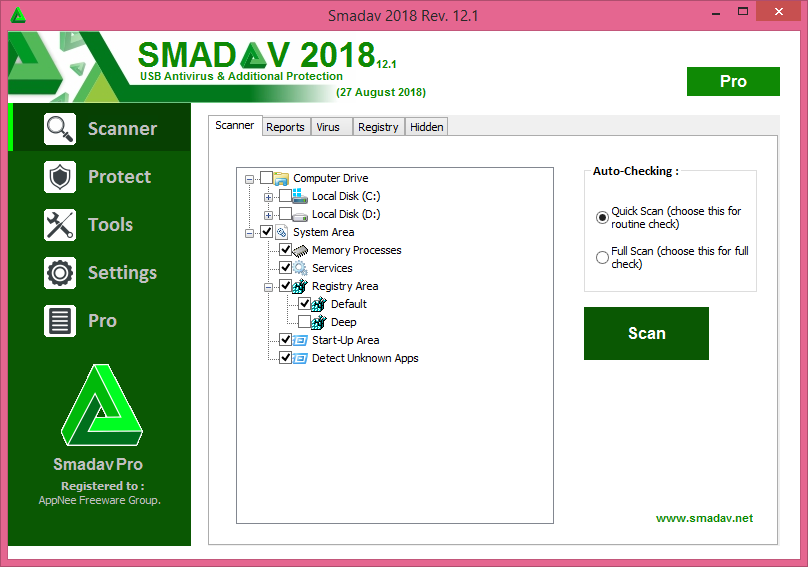
Continue reading [v15.x] Smadav – Dedicated to USB antivirus and additional protection