| Ⅰ | This article along with all titles and tags are the original content of AppNee. All rights reserved. To repost or reproduce, you must add an explicit footnote along with the URL to this article! |
| Ⅱ | Any manual or automated whole-website collecting/crawling behaviors are strictly prohibited. |
| Ⅲ | Any resources shared on AppNee are limited to personal study and research only, any form of commercial behaviors are strictly prohibited. Otherwise, you may receive a variety of copyright complaints and have to deal with them by yourself. |
| Ⅳ | Before using (especially downloading) any resources shared by AppNee, please first go to read our F.A.Q. page more or less. Otherwise, please bear all the consequences by yourself. |
| This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License. |

According to the developers of Tails: NSA (National Security Agency) has taken a number of approaches to put pressure on many free software projects and their developers. And, during a LinuxCon technology conference, the founder of Linux, Linus Torvalds revealed that the NSA hoped to install a backdoor in his operating system. In other words, for even Linux distributions, they are not absolutely safe now.
The “PRISM” event disclosing the top secret – electronic surveillance program of US government not only made Edward Snowden this person name become known all over the world, but also let an open-source operating system based on Debian Linux that he was using – Tails (short for The Amnesic Incognito Live System) gain considerable fame. Because Tails can escape the surveillance of the NSA. It is integrated by Amnesia (planned by Tor enthusiasts) project and Icognito system.
Tails is a live and portable Linux operating system (from Ireland, financial support is provided by the Tor Project) that can be installed on and direct booted from any bootable media (such as optical disc, USB flash drive, SD card, DVD), specially designed for people who care about their privacy very much. It is intended to help users anonymously surf the web and maximize their personal privacy protection. In order to achieve this goal, Tails builds in various tools for hiding identity (mainly Tor this anonymous proxy network), protecting privacy, and encrypting data or file, and does not store any data to the local system. Whether you’re a high-risk man (such as civil servant Edward Snowden, journalist Glenn Greenwald, and documentary producer Laura Poitras), or just a common user who hates being spied on and watched, you must know the existence of Tails OS!
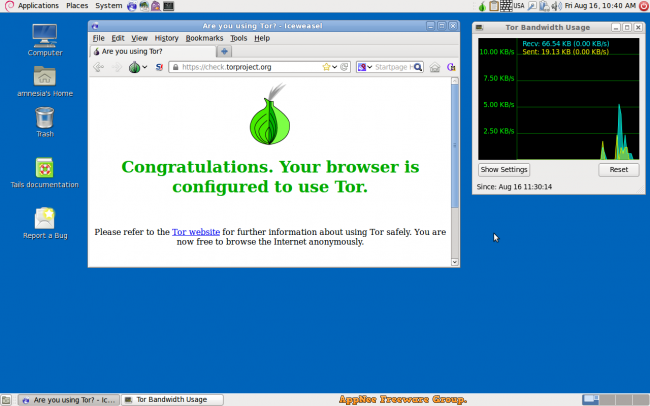
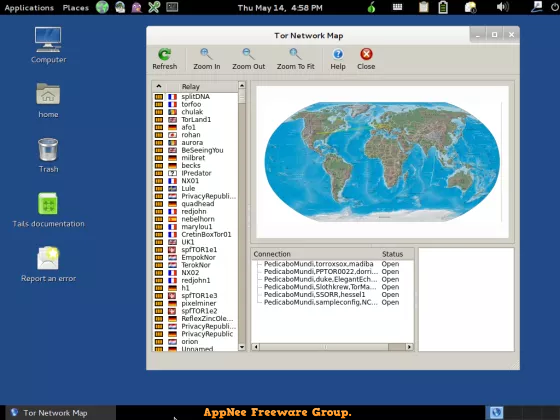
In Tails, system will run Tor automatically after startup. That means all outgoing connections will be forcibly established via Tor, and any direct (non-anonymous) connecting request will be blocked, so as to ensure that the Internet activity is extremely hard to track (your IP address, MAC address are all fake – this is so-called “anonymous”). In addition, in Tails, all files and data can be encrypted. What’s more, when Tails OS is shut down or restarted, the entire system returns to its original state. That is, everything you did in this OS will disappear immediately without leaving anything. The trouble is that you have to save what you want to keep with other storage devices (in fact, you can also separate a storage partition on your Tails bootable device). In the end, since all of the code of Tails is open-source, anyone with the ability or interest can check its security at any time.
I want to remind everybody: Although Tails also comes with some productive tools (such as OpenOffice, GIMP and Audacity), that does not mean it is suitable for everyday normal use. Because when the software and services you are using increase, the possibility of privacy disclosure will increase greatly too. As a result, Tails’ most suitable usage scenarios should be for anonymous communication, for example, the journalists need to protect their news sources. All in all, we spend most of our time on the Internet every day, but it is becoming more and more difficult to remain anonymous on the Internet. In other words, no operating systems such like Tails, we will have very few or even no privacy at all. In particular, under some circumstances that our OS has been implanted with backdoors by some institutions such as the NSA (National Security Agency) – they are sniffing and monitoring all our activities on the Internet.
// Key Features //
- Use the Internet anonymously and circumvent censorship, all connections to the Internet are forced to go through the Tor network
- Leave no trace on the computer you are using unless you ask it explicitly
- Use state-of-the-art cryptographic tools to encrypt your files, emails and instant messaging
// Prompts //
- Technical security is achieved mainly through two aspects: anonymity and encryption!
- Please bear in mind that, nothing is absolutely safe, and of course that include this Tails OS. In other words, it may also have some hidden “weaknesses” that might be exploited by attackers to make the computer running Tails lose anonymity (deanonymize) and even remotely execute malicious code.
// Related Links //
- Tails Official Documentation
- Tails Frequently Asked Questions
- Included software list in Tails
- Tails Installation Assistant
// Download URLs //
| License | Version | Download | Size |
| Freeware | Latest |  |
n/a |
(Homepage)
| If some download link is missing, and you do need it, just please send an email (along with post link and missing link) to remind us to reupload the missing file for you. And, give us some time to respond. | |
| If there is a password for an archive, it should be "appnee.com". | |
| Most of the reserved downloads (including the 32-bit version) can be requested to reupload via email. |