| Ⅰ | This article along with all titles and tags are the original content of AppNee. All rights reserved. To repost or reproduce, you must add an explicit footnote along with the URL to this article! |
| Ⅱ | Any manual or automated whole-website collecting/crawling behaviors are strictly prohibited. |
| Ⅲ | Any resources shared on AppNee are limited to personal study and research only, any form of commercial behaviors are strictly prohibited. Otherwise, you may receive a variety of copyright complaints and have to deal with them by yourself. |
| Ⅳ | Before using (especially downloading) any resources shared by AppNee, please first go to read our F.A.Q. page more or less. Otherwise, please bear all the consequences by yourself. |
| This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License. |
The Art of Deception is a bestseller about social engineering with nonprofit nature in 2002, written by the world famous hacker Kevin D. Mitnick who is also one of the headaches for FBI in the history (of course, after released from the federal prison in 2000 he became one of the world’s popular computer security experts).
In The Art of Deception, Kevin Mitnick will lead readers into the complex thinking of hackers. He described a large number of actual cheating scenarios, as well as social engineering attacks and consequences against enterprises. He focused on the human factor aspects relating to information security, explained why firewalls and encryption are not enough to prevent a smart attacker’s invasion to the database system of enterprise, also cannot prevent an angry employee to break down his company’s computer system. He illustrated: even for an information system with the most rigorous protection, in the face of a fraud artist determined, disguised as the IRS staff or other seemingly innocent roles, it will also become vulnerable.
The Art of Deception proceeded from attackers and victims two aspects, analyzed the reason that each kind of attack was able to have its way, and how to prevent these attacks. It has very attractive narration, as well as a strong readability, as if it is a detective novel introduces real criminal cases.
Most importantly, to compensate his past crimes, in this book Mitnick provided a number of guidelines as references for enterprises when they are in the development of safety behavior rules, training plans and safety manuals, so as to ensure that the high-tech security protection invested and built by company is not useless. He relied on his own experience, put forward many suggestions to prevent security vulnerabilities, and hoped that people don’t forget to watch out for the most serious safety hazards – the human nature.
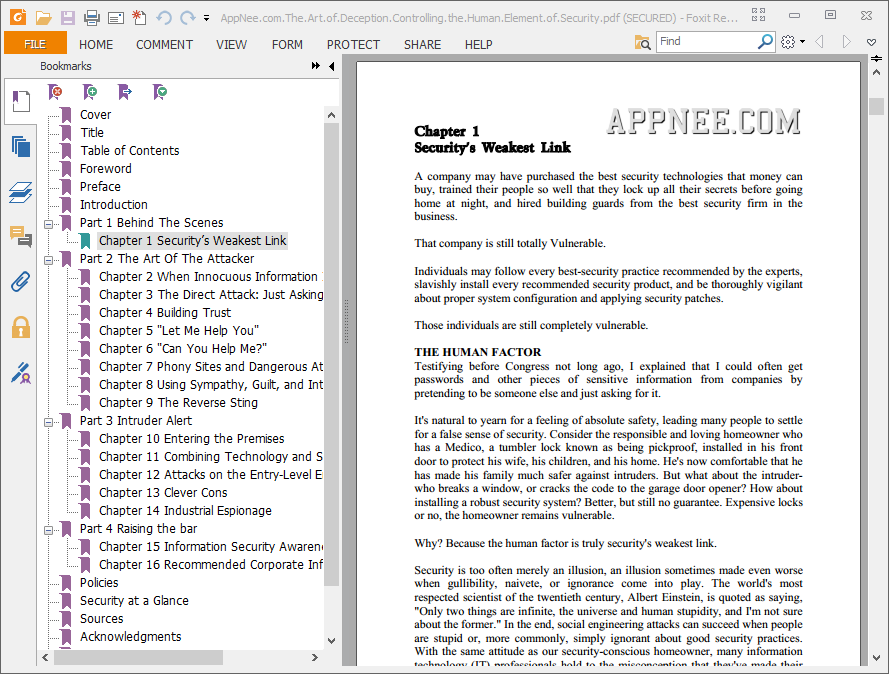
// Table Of Contents //
- Part 1: Behind the Scenes.
- Chapter 1: Security’s Weakest Link.
- Part 2: The Art of the Attacker.
- Chapter 2: When Innocuous Information Isn’t.
- Chapter 3: The Direct Attack: Just Asking for It.
- Chapter 4: Building Trust.
- Chapter 5: “Let Me Help You”.
- Chapter 6: “Can You Help Me?”.
- Chapter 7: Phony Sites and Dangerous Attachments.
- Chapter 8: Using Sympathy, Guilt, and Intimidation.
- Chapter 9: The Reverse Sting.
- Part 3: Intruder Alert.
- Chapter 10: Entering the Premises.
- Chapter 11: Combining Technology and Social Engineering.
- Chapter 12: Attacks on the Entry-Level Employee.
- Chapter 13: Clever Cons.
- Chapter 14: Industrial Espionage.
- Part 4: Raising the Bar.
- Chapter 15: Information Security Awareness and Training.
- Chapter 16: Recommended Corporate Information Security Policies.
- Security at a Glance.
// Download URLs //
 (1.49 MB | Homepage)
(1.49 MB | Homepage)
| If some download link is missing, and you do need it, just please send an email (along with post link and missing link) to remind us to reupload the missing file for you. And, give us some time to respond. | |
| If there is a password for an archive, it should be "appnee.com". | |
| Most of the reserved downloads (including the 32-bit version) can be requested to reupload via email. |