| Ⅰ | This article along with all titles and tags are the original content of AppNee. All rights reserved. To repost or reproduce, you must add an explicit footnote along with the URL to this article! |
| Ⅱ | Any manual or automated whole-website collecting/crawling behaviors are strictly prohibited. |
| Ⅲ | Any resources shared on AppNee are limited to personal study and research only, any form of commercial behaviors are strictly prohibited. Otherwise, you may receive a variety of copyright complaints and have to deal with them by yourself. |
| Ⅳ | Before using (especially downloading) any resources shared by AppNee, please first go to read our F.A.Q. page more or less. Otherwise, please bear all the consequences by yourself. |
| This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License. |
VeraCrypt is a free and open-source disk on-the-fly encryption (OTFE) software with strong security for Windows, Mac OS X and Linux platforms. It was developed by IDRIX from France, born as a branch of the highly-acclaimed but discontinued TrueCrypt project in 2013, but more outstanding than TrueCrypt.
Before TrueCrypt was killed due to more high-risk vulnerabilities (of which, the fatal weakness is that it could not withstand the brute force attack, and the root cause is its developers gave up update and repair, rather than the vulnerability itself), VeraCrypt had not attracted much attention from users. But at the same time as TrueCrypt officially declared its death, VeraCrypt managed to repair these vulnerabilities one by one. This made its exposure speed shoot up, so that VeraCrypt obtained the sustained growth of users (I guess they all came from TrueCrypt’s fan users).
Until now, VeraCrypt has become the only best disk encryption tool after TrueCrypt. Of course, another important factor is that other alternatives are either inferior and immature on quality to VeraCrypt, or not so complete and active as VeraCrypt on functions, such as CipherShed. When it comes to the classic PGP Desktop (short for: Pretty Good Privacy Desktop, and now called: Symantec Encryption Desktop), I’d like to say it’s not as small as VeraCrypt at least.
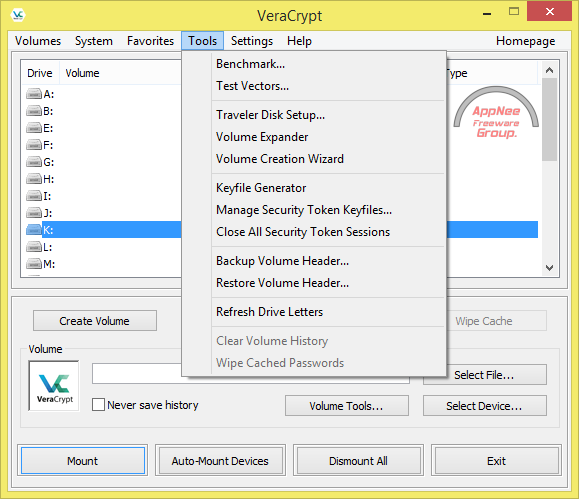
Although based on TrueCrypt, VeraCrypt greatly enhanced its encryption algorithm, meanwhile, it is fixing vulnerabilities continuously. Most importantly, it is still in a very active development and update, so we do not have to worry about its security problems. At any rate, we can make sure it is far better than TrueCrypt in this respect. Plus VeraCrypt takes the form of virtual disk to operate encrypted files, therefore the mobility of VeraCrypt has no problem too. Anyway, so far no organizations or individuals around the world claimed that they have successfully cracked the files encrypted by VeraCrypt.
// Key Features //
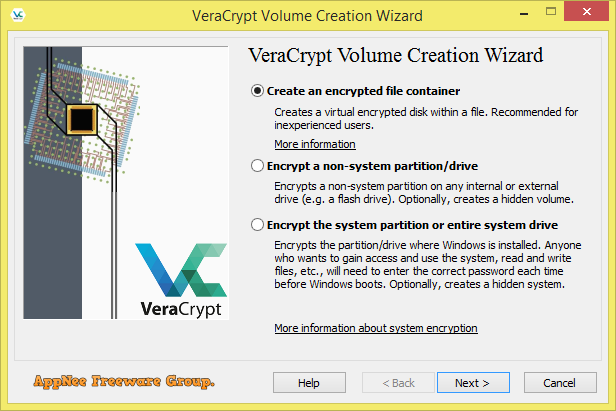
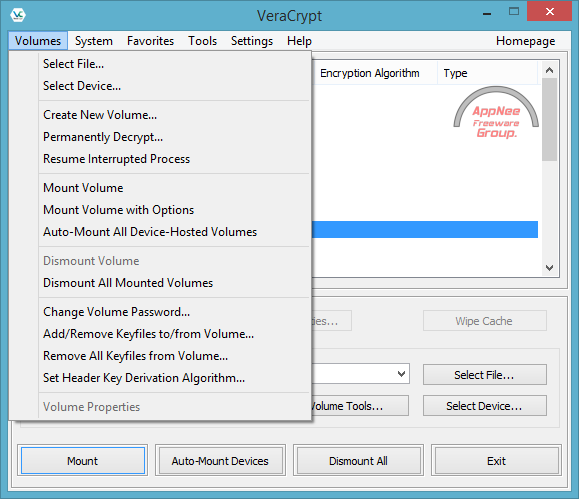
- Creates a virtual encrypted disk within a file and mounts it as a real disk
- Encrypts an entire partition or storage device such as USB flash drive or hard drive
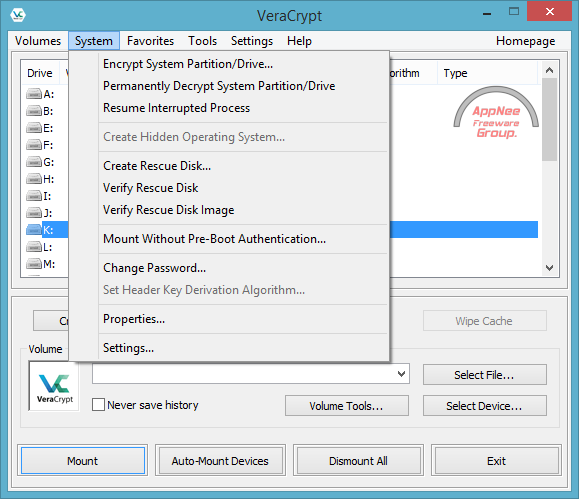
- Encrypts a partition or drive where Windows is installed (pre-boot authentication)
- Encryption is automatic, real-time(on-the-fly) and transparent
- Parallelization and pipelining allow data to be read and written as fast as if the drive was not encrypted
- Encryption can be hardware-accelerated on modern processors.
- Provides plausible deniability, in case an adversary forces you to reveal the password: Hidden volume (steganography) and hidden operating system
- Multiple encryption algorithms available
- Multiple languages support
- Complete free and open-source
// Prompts //
- Suggestion from AppNee: Never use Microsoft’s BitLocker Drive Encryption to encrypt any confidential files on Windows. This is because you can’t see the source code of any Microsoft programs so as to make sure they have not been implanted “backdoors” for the political or other purposes. On the contrary, the source code of open-source software are open and public, so it is difficult to hide any tricks such as backdoors.
- In order to dramatically increase the difficulty of brute force, VeraCrypt uses PBKDF2-RIPEMD160 algorithm to improve the iteration times of system partition and the iteration times of standard container & non-system partition to 327661 and 655331 respectively. As a consequence, the speed VeraCrypt opens an encrypted partition is slightly slower, and its encryption format is not compatible with TrueCrypt.
// Related Links //
// Download URLs //
| License | Version | Download | Size |
| Freeware | Latest |  (mir) (mir) |
n/a |
(Homepage | SourceForge)
| If some download link is missing, and you do need it, just please send an email (along with post link and missing link) to remind us to reupload the missing file for you. And, give us some time to respond. | |
| If there is a password for an archive, it should be "appnee.com". | |
| Most of the reserved downloads (including the 32-bit version) can be requested to reupload via email. |