| Ⅰ | This article along with all titles and tags are the original content of AppNee. All rights reserved. To repost or reproduce, you must add an explicit footnote along with the URL to this article! |
| Ⅱ | Any manual or automated whole-website collecting/crawling behaviors are strictly prohibited. |
| Ⅲ | Any resources shared on AppNee are limited to personal study and research only, any form of commercial behaviors are strictly prohibited. Otherwise, you may receive a variety of copyright complaints and have to deal with them by yourself. |
| Ⅳ | Before using (especially downloading) any resources shared by AppNee, please first go to read our F.A.Q. page more or less. Otherwise, please bear all the consequences by yourself. |
| This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License. |
Today, at this moment of rapid development of Internet and increasingly serious intrusion behaviors to network, the network security naturally became a focus in IT field. Accordingly, the network scanning technology has also become the most important one in this field. With help of Kali Linux OS’s built-in abundant powerful network scanning tools, each guy full of passion can become network security expert.
Network scanning is an advanced technology with extremely high operability. Through network scanning, we can find and grasp the distribution condition of all kinds of service ports opening on the target host, open services, service software along with its version and corresponding published vulnerabilities, and other aspects of safety related information, so as to initiate all necessary preparation for further network attacks. The basic flow of general network scanning and attack is as follows:
- Find a target host
- Open ports scanning
- Fingerprint information scanning
- Vulnerability scanning
- Implement penetration attacks
According to the general process above, Kali Linux Network Scanning Cookbook teaches you how to use a variety of tools in Kali Linux to implement network penetrations step by step. And when finish this book, you will master how to use many tools specially designed for network scanning and attack, including Scapy, Arping, Fping, NetDiscover, Metasploit, ICMP ping, Netcat, Nmap (NSE), Amap, xProbe2, Dmitry, p0f, Nessus, Burp Suite, snmpwalk, SSLScan, SSLyze, sqlmap, etc.
// Acquirable Skills //
- Develop a network-testing environment that can be used to test scanning tools and techniques
- Understand the underlying principles of network scanning technologies by building custom scripts and tools
- Perform comprehensive scans to identify listening on TCP and UDP sockets
- Examine remote services to identify type of service, vendor, and version
- Evaluate denial of service threats and develop an understanding of how common denial of service attacks are performed
- Identify distinct vulnerabilities in both web applications and remote services and understand the techniques that are used to exploit them
// Table Of Contents //
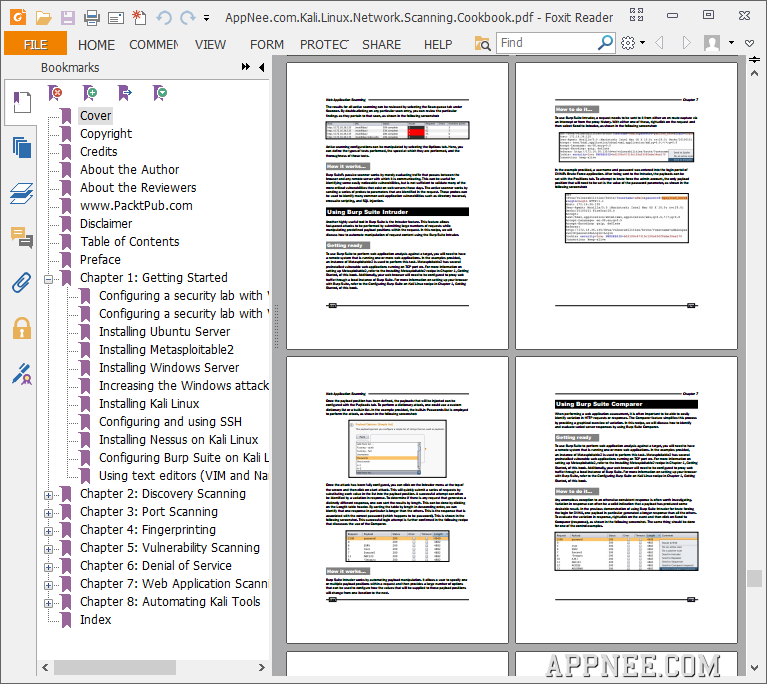
- Getting Started
- Discovery Scanning
- Port Scanning
- Fingerprinting
- Vulnerability Scanning
- Denial of Service
- Web Application Scanning
- Automating Kali Tools
// Book Example Codes //
// Download URLs //
 (4.57 MB | Homepage)
(4.57 MB | Homepage)
| If some download link is missing, and you do need it, just please send an email (along with post link and missing link) to remind us to reupload the missing file for you. And, give us some time to respond. | |
| If there is a password for an archive, it should be "appnee.com". | |
| Most of the reserved downloads (including the 32-bit version) can be requested to reupload via email. |