| Ⅰ | This article along with all titles and tags are the original content of AppNee. All rights reserved. To repost or reproduce, you must add an explicit footnote along with the URL to this article! |
| Ⅱ | Any manual or automated whole-website collecting/crawling behaviors are strictly prohibited. |
| Ⅲ | Any resources shared on AppNee are limited to personal study and research only, any form of commercial behaviors are strictly prohibited. Otherwise, you may receive a variety of copyright complaints and have to deal with them by yourself. |
| Ⅳ | Before using (especially downloading) any resources shared by AppNee, please first go to read our F.A.Q. page more or less. Otherwise, please bear all the consequences by yourself. |
| This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License. |
With the development of mobile devices and network, intelligent mobile phone has become a new paradise for hackers. Imagine, under this environment of everybody holds a smart phone nowadays, nothing is more active than the mobile phone viruses and the vulnerabilities’ exploits of software and mobile network. Therefore, to understand and master some practical security tools seems necessary and meaningful.
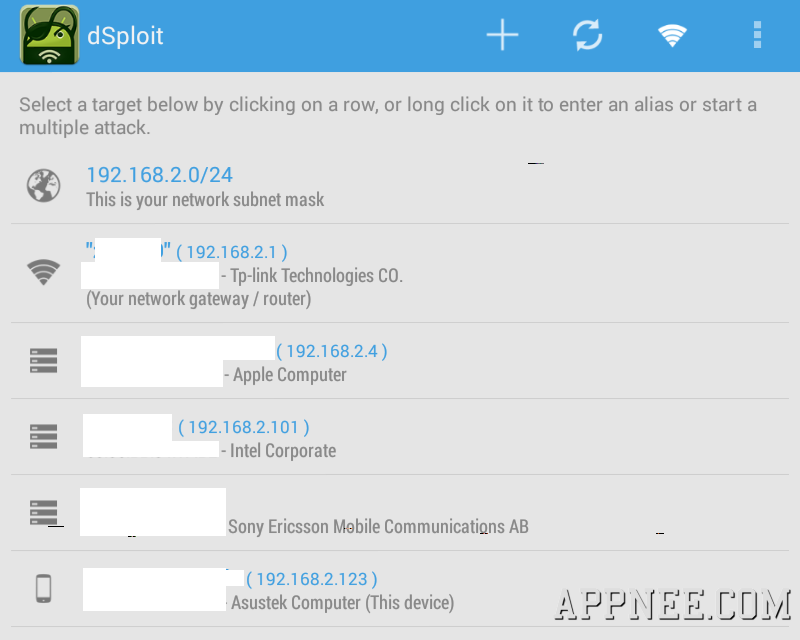
dSploit is a very powerful and popular professional penetration testing suite. In fact it’s also the only most complete and advanced one (it might be more appropriate to call it the hacker handy all-in-one toolkit) developed by Simone Margaritelli and sponsored by BackBox Linux (so when using you need to install the BusyBox) for Android OS, free and open source. AppNee likes to call it WiFi Killer!
Among similar apps (such as: zANTI, Network Spoofer, DroidSheep, FaceNiff, etc.), the only one comparable with dSploit is ZImperium‘s zANTI from Israel, yet zANTI’s biggest problem is it could not be popularized due to its commercial mode (although their function is almost the same, even zANTI has more beautiful UI and a few more and a little more powerful functions, such as password capturing and violent passwords guessing based on dictionary). But after merged with zANTI in 2014, they have a new version with name zANTI2, which will be released as a free and open source software soon (you can download here or here), that means both of them will get a better, more perfect development.
// Key Features //
| Feature | Detail |
| WiFi Cracking | The WiFi scanner will show in green access points with known default key generation algorithms, clicking on them allows you to easily crack the key |
| RouterPWN | Launch the RouterPWN service to pwn your router |
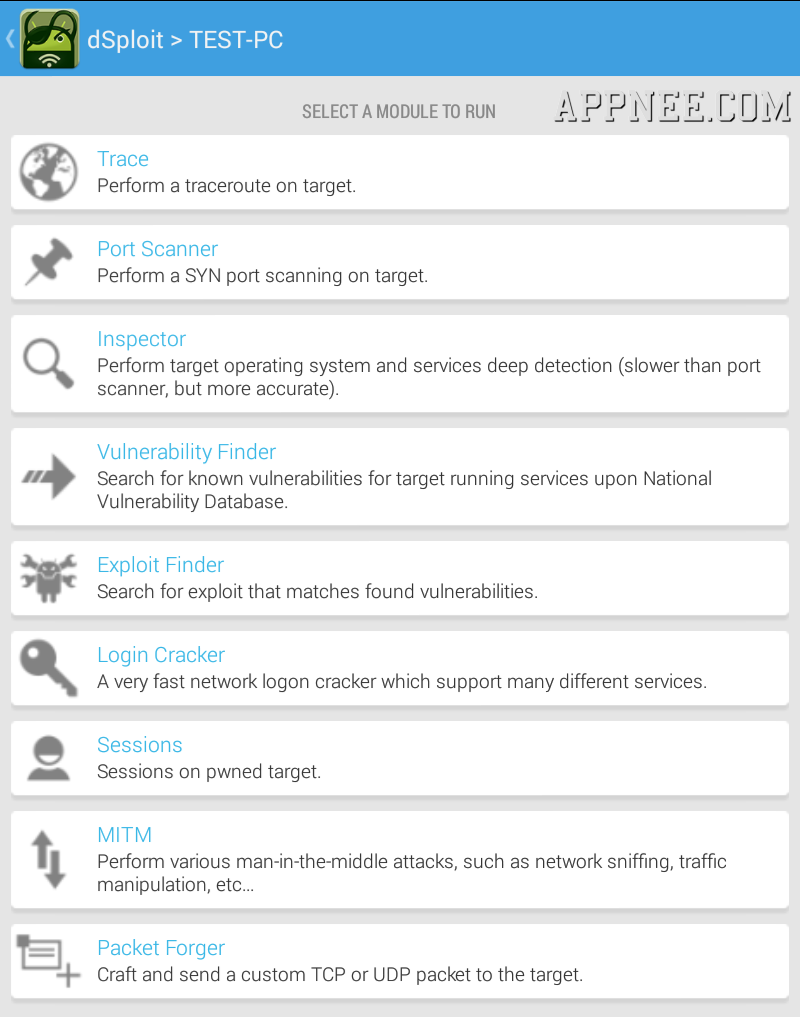
| Trace | Perform a traceroute on target |
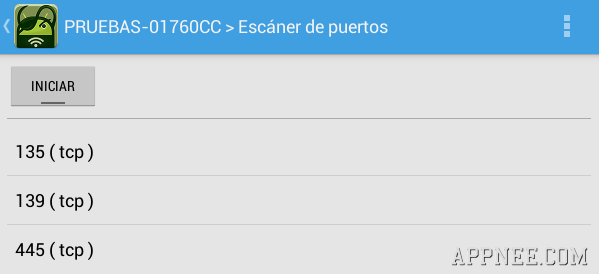
| Port Scanner | A syn port scanner to find quickly open ports on a single target |
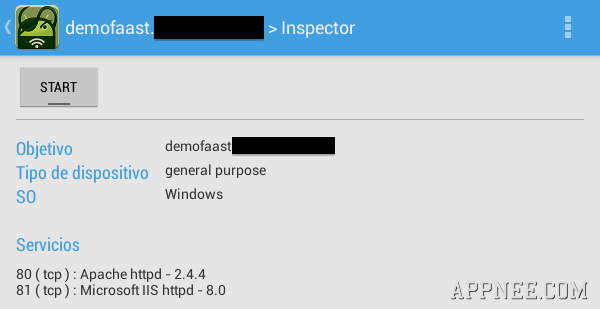
| Inspector | Performs target operating system and services deep detection, slower than syn port scanner but more accurate |
| Vulnerability Finder | Search for known vulnerabilities for target running services upon National Vulnerability Database |
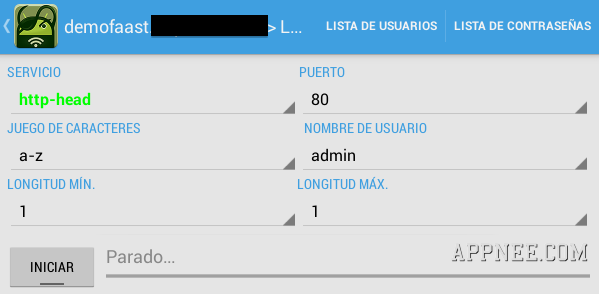
| Login Cracker | A very fast network logon cracker which supports many different services |
| Packet Forger | Craft and send a custom TCP or UDP packet to the target, such as Wake On LAN packets |
| Man In The Middle (MITM) | A set of man-in-the-middle tools to command&conquer the whole network |
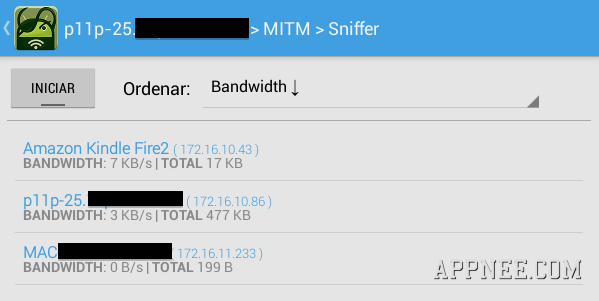
| Simple Sniff | Redirect target’s traffic through this device and show some stats while dumping it to a PCAP file |
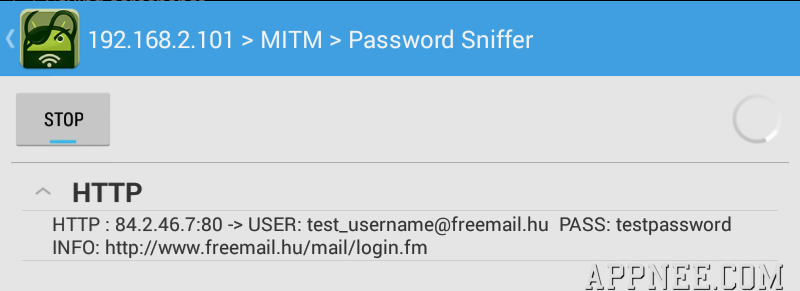
| Password Sniff | Sniff passwords of many protocols such as http, ftp, imap, imaps, irc, msn, etc from the target |
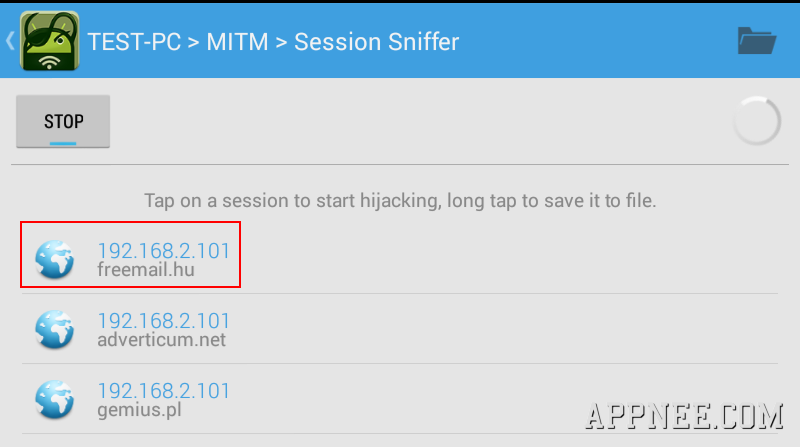
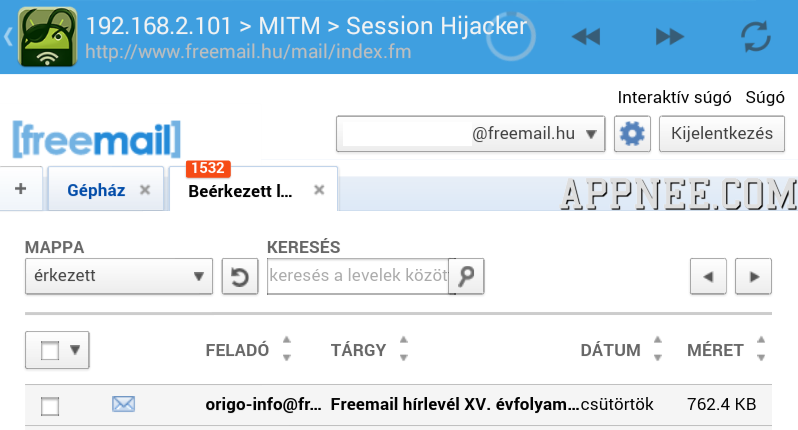
| Session Hijacker | Listen for cookies on the network and hijack sessions |
| Kill Connections | Kill connections preventing the target to reach any website or server |
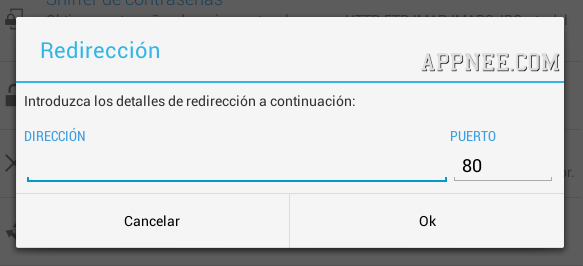
| Redirect | Redirect all the HTTP traffic to another address |
| Replace Images | Replace all images on webpages with the specified one |
| Replace Videos | Replace all YouTube videos on webpages with the specified one |
| Script Injector | Inject a JavaScript in every visited webpage |
| Custom Filter | Replace custom text on webpages with the specified one |
// Main Applications //
- WiFi Scanning & Common Router Key Cracking
- Deep Inspection
- Vulnerability Search
- Multi Protocol Login Cracker
- Packet Forging with Wake On Lan Support
- HTTPS/SSL Support ( SSL Stripping + HTTPS -> Redirection )
- MITM Realtime Network Stats
- MITM Multi Protocol Password Sniffing
- MITM HTTP/HTTPS Session Hijacking HTTP/HTTPS
- MITM HTTP/HTTPS Hijacked Session File Persistance HTTP/HTTPS
- MITM HTTP/HTTPS Realtime ManipulationHTTP / HTTPS
// System Requirements //
- Android device should be 2.3+ with ARM CPU.
- Android OS must be rooted.
- Must have a full install of BusyBox, i.e. make sure you have its every utility installed
// Edition Statement //
AppNee provides everyone two key versions of dSploit: v1.0.31 full version and v1.1.3 the last nightly build version (joined the Metasploit framework on the basis of the full version, which enables to perform attacks after detection). You can decide to use these old versions or just download the latest zANTI2 in order to get the latest code updates and features.
Nightly Build v1.1.3b (20140130):
- new upgrade service ( uses notifications )
- tools can now compiled using the android NDK
- tools is built statically ( solves LD_LIBRARY_PATH bug )
- improved the way we use root shells ( a lot improved )
- now inspector can be run without the port scanner
- some UI elements modifications
- created a PreferenceActivity for manage options of MSF modules
- Session class allow us to handle MSF opened sessions
- created a very poor shell interface ( for opened MSF sessions )
*** Nightly releases could be extremely unstable.
// Prompts //
dSploit can only work in landscape mode, if forced rotating screen it will lead to a crash.
// Warning //
Due to the nature of work, dSploit might be reported as malware (PUP: Android:DSploit-E [Tool] with low severity) in some mobile security apps. Just add it to the ignore list, it is safe.
// Download URLs //
| Edition | Version | Download | Size |
| Full Stable | v1.0.31 |  |
6.38 MB |
| Nightly Build | v1.1.3b |  |
10.5 MB |
| v1.1.3c |  |
11.4 MB |
(No Homepage)
| If some download link is missing, and you do need it, just please send an email (along with post link and missing link) to remind us to reupload the missing file for you. And, give us some time to respond. | |
| If there is a password for an archive, it should be "appnee.com". | |
| Most of the reserved downloads (including the 32-bit version) can be requested to reupload via email. |