| Ⅰ | This article along with all titles and tags are the original content of AppNee. All rights reserved. To repost or reproduce, you must add an explicit footnote along with the URL to this article! |
| Ⅱ | Any manual or automated whole-website collecting/crawling behaviors are strictly prohibited. |
| Ⅲ | Any resources shared on AppNee are limited to personal study and research only, any form of commercial behaviors are strictly prohibited. Otherwise, you may receive a variety of copyright complaints and have to deal with them by yourself. |
| Ⅳ | Before using (especially downloading) any resources shared by AppNee, please first go to read our F.A.Q. page more or less. Otherwise, please bear all the consequences by yourself. |
| This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License. |
As we all know, Freenet famously led to the popularity of the dark web before Tor was released. Today, there have been many dark web systems, large and small. Freenet, Tor and I2P are known as the three giants in dark web, and thereinto Tor has the largest user base. In essence, Tor (short for The Onion Router) is a free software designed to realize the anonymous Internet communication.
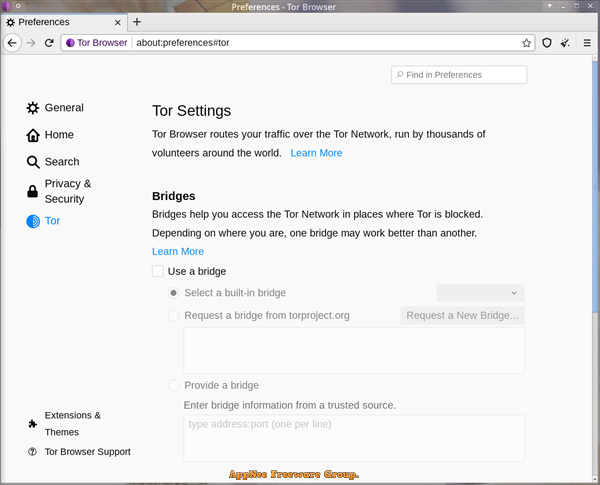
Through Tor, users can connect to an overlay network consists of thousands of relays provided by volunteers from around the world for free, so as to achieve the purposes of hiding the real address of users, avoiding Internet surveillance and traffic analysis. As a result, Tor users’ Internet activities (including browsing online websites and posts, Instant Messaging, and other communication forms) are fairly difficult to track. Of course, Tor was originally designed to protect users’ personal privacy, as well as the freedom and ability to communicate secretly without being monitored.
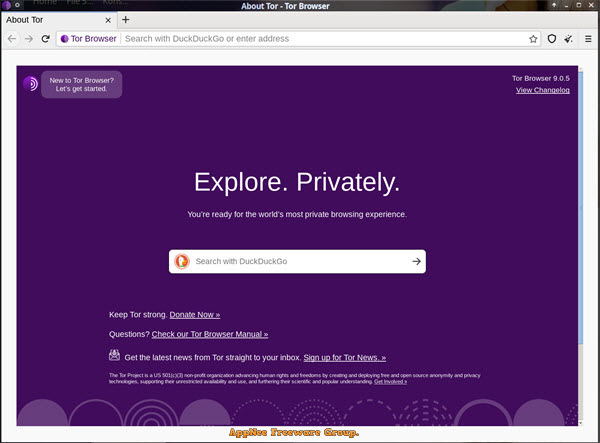
Tor Browser (formerly known as Tor Browser Bundle, TBB for short) is the flagship product of the entire Tor project that was created by Steven Murdoch in 2008. It was modified based on the Mozilla Firefox ESR browser, and has been tweaked a lot for security and privacy protection by the Tor Project developers. Tor Browser has built-in extensions such as TorButton, TorLauncher, NoScript, HTTPS Everywhere and Tor proxy, is released as free, open-source and portable software, and can run on a variety of operating systems, including Windows, Mac, Linux, Unix, Android.
In terms of working mechanism, Tor Browser starts the Tor process in the background and connects to the Internet through it. Once the program is disconnected, Tor Browser automatically deletes all private, sensitive data, such as cookies and browsing history. The software itself provides a SOCKS proxy service through which some applications can already use the Tor network. When used in combination with proxy server software such as Privoxy, Tor Browser enables all networking applications that utilize the HTTP/HTTPS protocol, as well as all applications that can set up an HTTP/HTTPS proxy to connect to the Internet via the Tor network.
// Key Features //
| Block Trackers |
| Tor Browser isolates each website you visit so third-party trackers and ads can’t follow you. Any cookies automatically clear when you’re done browsing. So will your browsing history. |
| Defend Against Surveillance |
| Tor Browser prevents someone watching your connection from knowing what websites you visit. All anyone monitoring your browsing habits can see is that you’re using Tor. |
| Resist Fingerprinting |
| Tor Browser aims to make all users look the same, making it difficult for you to be fingerprinted based on your browser and device information. |
| Multi-layered Encryption |
| Your traffic is relayed and encrypted three times as it passes over the Tor network. The network is comprised of thousands of volunteer-run servers known as Tor relays. |
| Browse Freely |
| With Tor Browser, you are free to access sites your home network may have blocked. |
// Download URLs //
| License | Version | Download | Size |
| Freeware | Latest |  |
n/a |
(Homepage)
| If some download link is missing, and you do need it, just please send an email (along with post link and missing link) to remind us to reupload the missing file for you. And, give us some time to respond. | |
| If there is a password for an archive, it should be "appnee.com". | |
| Most of the reserved downloads (including the 32-bit version) can be requested to reupload via email. |