| Ⅰ | This article along with all titles and tags are the original content of AppNee. All rights reserved. To repost or reproduce, you must add an explicit footnote along with the URL to this article! |
| Ⅱ | Any manual or automated whole-website collecting/crawling behaviors are strictly prohibited. |
| Ⅲ | Any resources shared on AppNee are limited to personal study and research only, any form of commercial behaviors are strictly prohibited. Otherwise, you may receive a variety of copyright complaints and have to deal with them by yourself. |
| Ⅳ | Before using (especially downloading) any resources shared by AppNee, please first go to read our F.A.Q. page more or less. Otherwise, please bear all the consequences by yourself. |
| This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License. |
Ghidra is a free and open-source software reverse engineering (SRE) framework for Windows, Mac and Linux platforms, developed and maintained by the NSA (National Security Agency) of United States in 2019, written in Java. It is regarded as currently the only thing that can compete with IDA Pro by many security researchers and software developers.
As the creator of the famous Industrial Control Systems (ICS) malware Stuxnet, NSA originally developed Ghidra to train reverse engineers who study and create malware. This move allows more people to learn reverse engineering without paying IDA Pro’s high licensing fees, and directly disrupts the market for reverse engineering tools long dominated by IDA Pro.
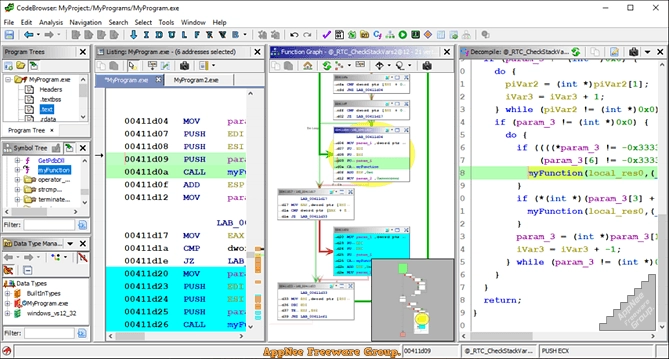
Ghidra includes a suite of full-featured advanced software source code analysis tools, enabling users to analysis compiled code on various platforms. It provides features like code browsing, program difference comparison, disassembly and assembly, decompilation, drawing and scripting, supports a variety of processor instruction sets and executable file formats, can run under the user interaction and automation modes, allows users to develop their own plug-ins and scripts using public APIs, as well as hundreds of other features. In addition, Ghidra supports headless mode, in which researchers can add any number of cloud instances to perform large-scale reverse engineering. It can also be deployed as a peripheral-free server for teams to efficiently collaborate and reverse-engineer large files.
Although Ghidra won’t change the way many companies work any time soon, it does lower the barrier to entry for reverse engineering and help train a new generation of reverse engineers. So in the long run, as the Ghidra ecosystem continues to grow, it will slowly eat away IDA Pro’s existing market share and accelerate the demise of other competitors in the market. As a discipline, reverse engineering has a steep learning curve, but Ghidra is easy to get started with. So, if you want to start the journey of reverse engineering, Ghidra is the first choice with a very low threshold of entry.
// Supported Architectures //
The following architectures or binary formats are supported:
// Official Demo Video //
// System Requirements //
- JDK 11 64-bit
- Gradle 6.8+ or 7.x
- make, gcc, and g++ (Linux/macOS-only)
- Microsoft Visual Studio (Windows-only)
// Related Links //
// Download URLs //
| License | Version | Download | Size |
| Freeware | Latest |  |
n/a |
| If some download link is missing, and you do need it, just please send an email (along with post link and missing link) to remind us to reupload the missing file for you. And, give us some time to respond. | |
| If there is a password for an archive, it should be "appnee.com". | |
| Most of the reserved downloads (including the 32-bit version) can be requested to reupload via email. |