| Ⅰ | This article along with all titles and tags are the original content of AppNee. All rights reserved. To repost or reproduce, you must add an explicit footnote along with the URL to this article! |
| Ⅱ | Any manual or automated whole-website collecting/crawling behaviors are strictly prohibited. |
| Ⅲ | Any resources shared on AppNee are limited to personal study and research only, any form of commercial behaviors are strictly prohibited. Otherwise, you may receive a variety of copyright complaints and have to deal with them by yourself. |
| Ⅳ | Before using (especially downloading) any resources shared by AppNee, please first go to read our F.A.Q. page more or less. Otherwise, please bear all the consequences by yourself. |
| This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License. |
The biggest trouble with working or studying on a public computer is that there will always be people who will look into and even steal, delete your important documents, materials and data without permission, some of which may even involve personal privacy and trade secrets. In this case, you can use Hidden Disk to create a virtual, encrypted drive (you need a password to access it) that can be hidden at will to solve this problem perfectly.
Unlike other similar programs, Hidden Disk does not simply encrypt or lock the original drive/partition. Instead, it additionally creates a new, virtual storage space, then allows us to store private data and files in this hidden partition, and finally locks it with a password you set. This undoubtedly strengthens the access control to this private space from multiple levels, and has guaranteed both the data security in this partition and the protection of user’s privacy adequately.
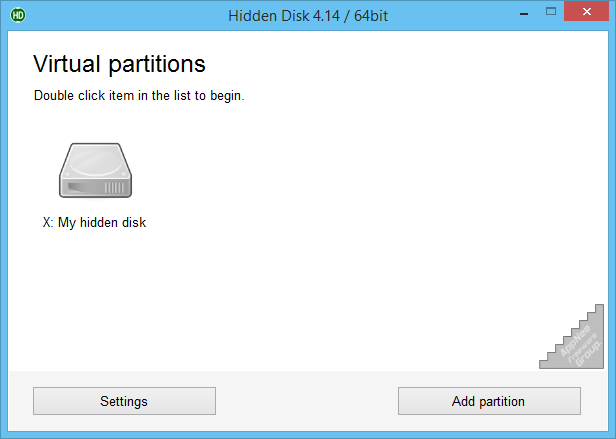
To read/write files in this hidden disk, you must first open Hidden Disk and enter the correct password, then the hidden drive/partition will appear. In addition, Hidden Disk allows many hidden disk partitions to be created in one computer, and we are able to set different passwords for them, so that different drives can be used to store and manage important data of different natures, types or levels.
// Key Features //
- Virtual disk to store your secret files. No need to buy any new hardware
- Create and use your own password to access your secret disk
- You can hide secret disk in a second and in case of power failure it will automatically become invisible
- Creates more than one virtual disk and separate storage for each task
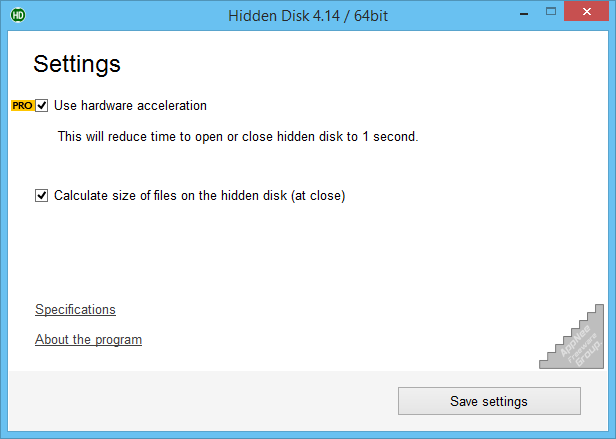
- Even more protection-use or disable PIN code to access the program
- Access to many options located throughout the program. Provides maximum convenience and security to users of this app
- Access to the additional options to customize the look and style of the program
// Edition Statement //
AppNee provides the Hidden Disk Professional Edition multilingual full installers and CyRobo all products all versions universal activator for Windows 32-bit & 64-bit.
// Installation Notes //
- Download and install the latest version of Hidden Disk from official site
- Exit program
- Run the universal activator, and select ‘Hidden Disk‘ from the “Product” list (and set the right version number, if needed)
- Click ‘Activate‘
- Done
*** You’d better don’t check for updates, and block this program with your firewall.
// Prompts //
- Hidden disk will appear as a separate hard disk in My Computer. You can work with it as you would with a regular disk. You can hide it instantly, without damaging the contents.
- Due to system’s limitations, the hidden disk uses free space on the system disk. Do not reinstall Windows; and do not format the system disk.
// Related Links //
// Download URLs //
| License | Version | Download | Size |
| Free Edition | Latest |  |
n/a |
| Universal Activator | |||
| Professional Edition | v1.x, v2.x, v3.x, v4.x, v5.x |  |
72.8 KB |
(Homepage)
| If some download link is missing, and you do need it, just please send an email (along with post link and missing link) to remind us to reupload the missing file for you. And, give us some time to respond. | |
| If there is a password for an archive, it should be "appnee.com". | |
| Most of the reserved downloads (including the 32-bit version) can be requested to reupload via email. |