| Ⅰ | This article along with all titles and tags are the original content of AppNee. All rights reserved. To repost or reproduce, you must add an explicit footnote along with the URL to this article! |
| Ⅱ | Any manual or automated whole-website collecting/crawling behaviors are strictly prohibited. |
| Ⅲ | Any resources shared on AppNee are limited to personal study and research only, any form of commercial behaviors are strictly prohibited. Otherwise, you may receive a variety of copyright complaints and have to deal with them by yourself. |
| Ⅳ | Before using (especially downloading) any resources shared by AppNee, please first go to read our F.A.Q. page more or less. Otherwise, please bear all the consequences by yourself. |
| This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License. |

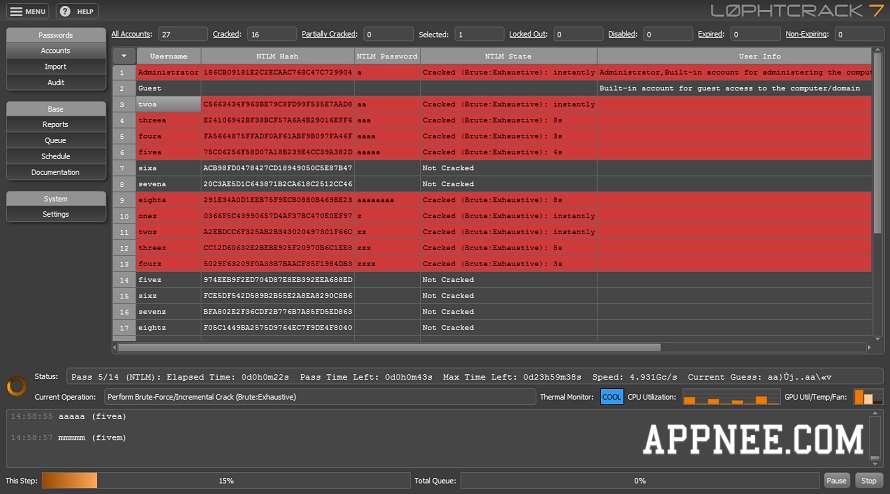
The god knows who is using L0phtCrack as a security auditing tool to do the so-called password strength testing or recovery. I conclude that 90% of individuals are using it to violently obtain the passwords itself (through methods of dictionary, brute-force, hybrid attacks, rainbow tables, etc.). Whatever you’s like to use it for, what we just can’t deny is that it’s the most outstanding one in similar software.
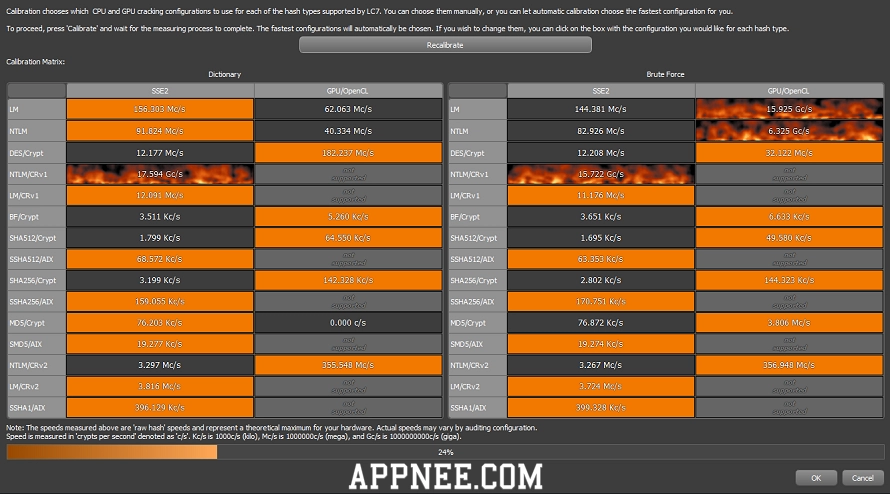
As a network/system administrator’s essential password audit and recovery tool, L0phtCrack (full name: L0phtCrack Password Auditor) can be used to detect whether the Windows/UNIX users’ passwords are secure enough or not. Meanwhile, it’s also the best and fastest Winodws/UNIX administrator account’s password cracking tool (as it turns out, the simple or prone to being cracked administrator password is one of the biggest security threats, because in most cases, the attackers logged in the computer as a legal identity is often very difficult to detect).
L0phtCrack official describes it to be a password auditing and recovery tool providing two critical capabilities to system administrators, but AppNee always believes it has only one original design purpose: password cracking – and it has been characterized as a professional level of hacking tool.
// Key Features //
- Password Scoring
- Supports pre-computed password hashes (dictionary)
- Windows & Unix Password Support
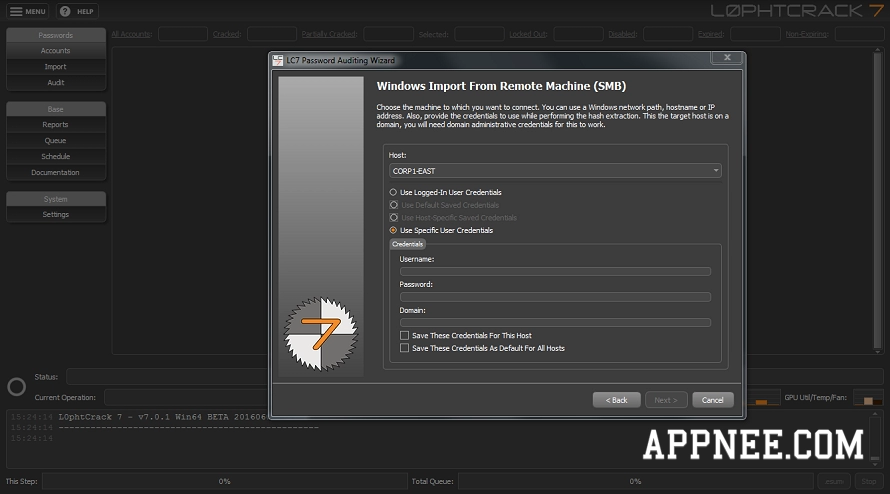
- Remote password retrieval
- Scheduled Scans
- Remediation assistance against accounts with poor passwords
- Updated Vista/Windows 7 Style UI
- Executive Level Reporting
- Password Risk Status
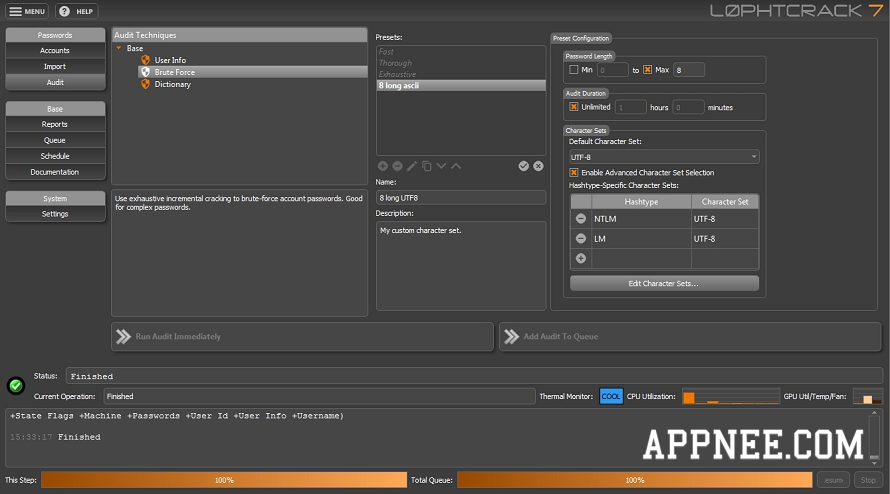
- 4 Password Audit Methods: Dictionary, Hybrid, Precomputed, and Brute Force
- Password Character Sets (including Alpha, Alphanumeric, Alphanumeric/Symbol, Alphanumeric/Symbol/International)
- Password Length Distribution
- Summary Report
- Foreign Password Cracking
// Range of Target Systems //
- Runs On Windows XP and higher
- Operates on networks with Windows NT, 2000, XP, Server 2003 R1/R2, Server 2008 R1/R2, on 32- and 64-bit environments, as well as most BSD and Linux variants with an SSH daemon
// System Requirements //
- Microsoft Visual C++ 2013 Redistributable (x86/x64)
// Official Demo Video //
// Registration Codes //
| Name | Key |
| Accipiter | 000014-WM6N2A-TGRKT6-DZXJHB-ZJNZV7-KYPNMP-68YFN7-GT2FBF-U647XA-NF2R2W |
| 000014-WM6N2A-TGRNNR-PXYAY7-JYNZUP-TMCTBT-8WVHR5-B98K5C-UJCNHD-P17BJ2 | |
| 000014-WM6N2A-TGRQDY-7Y61VT-8T5YTZ-0MJQ7K-25YGMF-5HQHX8-A77VWW-D64GKA | |
| 000014-WM6N2A-TGRMDP-ZADATZ-YAE8B7-MGX4VX-RBPQTX-DJ6J7H-QK86CX-BAAQ8B | |
| 000014-WM6N2A-TGRG7M-GZV33F-ZTDJFA-ARJVQ6-7DF4MZ-H5Q5T3-T3B3Z2-4309MY |
*** These keys are only working for L0phtCrack v6.0.18.
// Edition Statement //
AppNee provides the L0phtCrack portable full registered versions, full installers along with activation codes, unlocked files or license files for Windows 32-bit and 64-bit.
// Installation Notes //
for v7.1.x:
- Download and install L0phtCrack
- Run program, click ‘Activate License‘
- Run key maker, enter your desired strings, then click ‘Gen‘ and save the license file (.cdm) on desktop
- Go back to program, enter your activation code (Name -> License Name, Serial -> Activation Code) and click ‘Activate Offline‘
- Click ‘Browse For CDM File…‘, and select your license file on desktop
- Click ‘Activate Offline Using CDM File‘
- Done
for v7.0.14+:
- Just download and extract to use!
for v6.0.17, v6.0.18:
- Download and setup the official installer
- Copy the unlocked file (lc.exe or lc7core.dll) to L0phtCrack’s installation directory and overwrite
- All done for version v6.0.17, but for version v6.0.18, you also need to use one registration code above to activate!
// Tips //
In fact, if you want to get the passwords of people we can come into contact with in our life, using social engineering actually is much more efficient and easier than any tools. In particular, quite often, the commonly used passwords must be simple or easy to remember.
// Related Links //
// Download URLs //
| License | Version | Type | Download | Size |
| Freeware | Latest | Setup |  |
n/a |
| Enterprise Edition | v6.0.18 | Setup | reserved | 16.6 MB |
| v7.0.16 | Portable | reserved | 57.2 MB | 62.1 MB | |
| v7.1.6 | Setup | reserved | 67.4 MB | 73.1 MB |
| If some download link is missing, and you do need it, just please send an email (along with post link and missing link) to remind us to reupload the missing file for you. And, give us some time to respond. | |
| If there is a password for an archive, it should be "appnee.com". | |
| Most of the reserved downloads (including the 32-bit version) can be requested to reupload via email. |