| Ⅰ | This article along with all titles and tags are the original content of AppNee. All rights reserved. To repost or reproduce, you must add an explicit footnote along with the URL to this article! |
| Ⅱ | Any manual or automated whole-website collecting/crawling behaviors are strictly prohibited. |
| Ⅲ | Any resources shared on AppNee are limited to personal study and research only, any form of commercial behaviors are strictly prohibited. Otherwise, you may receive a variety of copyright complaints and have to deal with them by yourself. |
| Ⅳ | Before using (especially downloading) any resources shared by AppNee, please first go to read our F.A.Q. page more or less. Otherwise, please bear all the consequences by yourself. |
| This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License. |
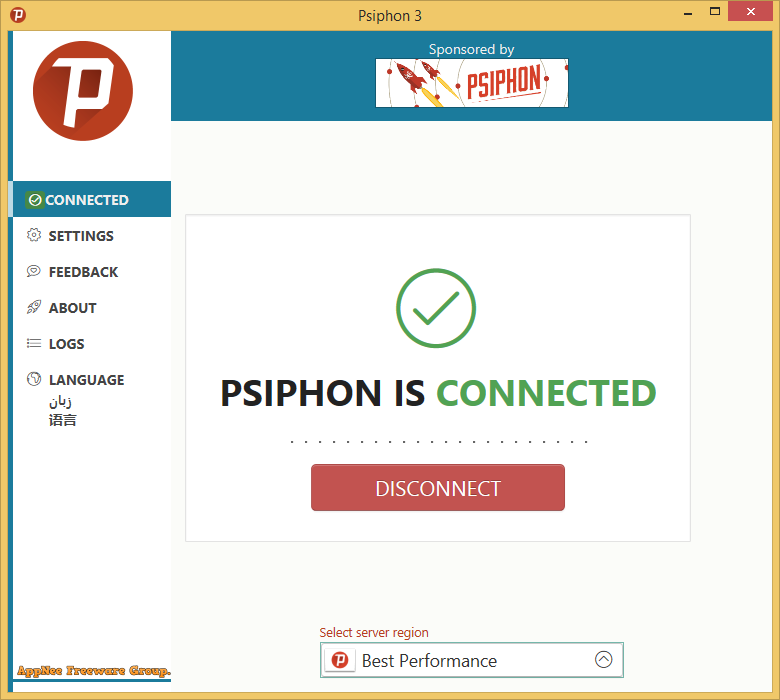
Sometimes when you are traveling, studying or working overseas, you will inevitably need to visit some blocked websites in that country. To access to your favorite news broadcast or social media platforms in some countries with censorship mechanism, in addition to using the traditional, old-fashioned VPN springboard circumvent the blocks, there are more and more Internet proxy tools available to enable users to quickly evade the Internet censorship. Psiphon is one of the best.
Continue reading [v3.181, v393] Psiphon – Free and open-source Internet Freedom VPN tool